The Shared Responsibility Model is a foundational security framework used by all major cloud providers today.
It clarifies which security tasks belong to the cloud provider and which belong to the customer.
Understanding this model is essential for designing secure architectures and preventing misconfigurations in modern cloud environments.
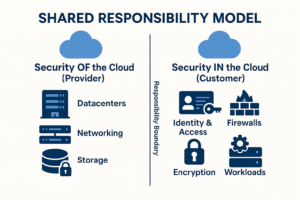
Security responsibilities in cloud computing are divided into two major areas:
Security of the Cloud and Security in the Cloud.
While they sound similar, they cover completely different layers of the architecture.
Security Of the Cloud (Cloud Provider Responsibility)
Security of the cloud refers to what the cloud provider must secure.
This includes the core infrastructure that runs all cloud services.
The customer does not have any access to these layers, so the provider must guarantee their confidentiality, integrity, and availability.
Technical Responsibilities Include:
- Physical datacenter security: biometric access, CCTV, on-site security teams
- Hardware integrity: servers, storage appliances, network devices
- Virtualization and hypervisor security: ensuring isolation between tenants
- Global network backbone: secure routing, DDoS resilience, redundant fiber paths
- Firmware and infrastructure patching: routers, switches, storage controllers
- Power, cooling, and environmental controls
- Secure hardware lifecycle management: supply chain verification and secure disposal
In other words, the provider secures everything that forms the foundation of the cloud platform.
Security In the Cloud (Customer Responsibility)
Security in the cloud refers to everything the customer is required to secure within the cloud environment.
Although the provider protects the infrastructure, the customer is responsible for how workloads are configured, deployed, and accessed.
Technical Responsibilities Include:
- Identity & Access Management (IAM): account permissions, MFA, least privilege enforcement
- Network configuration: virtual networks, segmentation, firewalls, routing rules
- Data protection: encryption, key management, secret rotation
- Compute workload hardening: VM OS patching, container security, runtime defense
- Application security: authentication, API authorization, input validation
- Monitoring & logging: SIEM integration, log retention, anomaly detection
- Backup & disaster recovery strategies: snapshots, replication, failover planning
- Compliance implementation: aligning workloads with regulatory standards
The customer owns the security of everything they deploy or configure inside the cloud.
Comparison Table: Security Of the Cloud vs Security In the Cloud
| Aspect | Security Of the Cloud (Provider) | Security In the Cloud (Customer) |
|---|---|---|
| Datacenter Protection | Provider secures physical buildings and hardware | Not applicable |
| Core Networking | Provider secures backbone, routers, cross-region connectivity | Customer configures routing, firewall rules, segmentation |
| Virtualization Layer | Provider maintains hypervisor and tenant isolation | Customer manages guest OS and application settings |
| Data Encryption | Provider ensures physical media-level encryption | Customer manages encryption policies, key rotation, KMS usage |
| Access Control | Provider secures backend IAM infrastructure | Customer defines roles, policies, and authentication flows |
| Application Security | Not applicable | Customer secures code, APIs, dependencies, and runtime |
| Monitoring | Provider ensures platform logs exist | Customer configures alerting, SIEM pipelines, incident response |
On-Premises vs Cloud Security Responsibilities
| Security Component | On-Premises | Cloud |
|---|---|---|
| Physical Security | Organization must secure buildings, racks, and hardware | Cloud provider fully manages physical layers |
| Hardware Ownership | Owned and maintained by the organization | Provided and maintained by the cloud provider |
| OS Patching | Organization patches hypervisors and OS manually | Provider patches hypervisors; customer patches OS for VMs |
| Networking | Full physical & logical network design required | Provider handles core network; customer configures virtual network |
| High Availability | Requires multiple sites, redundant power, cooling | Native multi-region and multi-zone capabilities available |
| Compliance | Everything must be self-implemented | Provider offers compliance baseline; customer configures workload compliance |
Why This Model Matters
Most cloud-related security incidents are not caused by the cloud provider, but by customer-side misconfigurations.
Common failures include:
- Exposed storage buckets
- Overly permissive firewall rules or network policies
- Unpatched virtual machines
- Leaked API keys or secrets in code repositories
- Incorrect IAM role configurations
By clearly understanding where responsibilities are divided, organizations can design stronger security architectures, reduce attack surfaces, and maintain compliance across the cloud ecosystem.
Conclusion
The Shared Responsibility Model is essential for secure cloud architectures.
Cloud providers secure the platform infrastructure, while customers secure everything they run within that platform.
Mastering this distinction ensures safer deployments, improved operational security, and better resilience in modern cloud environments.
Views: 24